- Detect known and unknown threats by leveraging the vast amount of data gathered from endpoints
- Protect against malware with signature-free AI / machine learning engines
- Behavior detection technology protects against fileless attacks
Security CrowdStrike Function
Endpoint security solutions that address threat risk with Next Generation Antivirus, EDR (Endpoint Detection and Response) and threat hunting.

Falcon Prevent

Block attacks that cannot be protected by AV
The latest AI and machine learning engines prevent fileless attacks, exploits and more. In addition to IOC (Indicator of Compromise), IOA (Indicator of Attack) can be used, and behavioral blocks can be used by AV.
High defense
The av-comparatives Real-World Protection Test (August-November) showed high performance with a block rate of 99.9%. (Note)
Lightweight agent
No need for tasks that significantly degrade performance, such as signature updates or disk scans. A lightweight agent of about 25 MB with less than 1% CPU utilization. It’s a lightness that users don’t realize the agent is in.
Note) Business Security Test 2022 (August - November) - AV-Comparatives
Falcon Insight
- Detects a wide range of known and unknown threats, from malware to fileless attacks
- Remotely isolate and repair hosts from the management console
- Investigate alerts by alert and multiple alerts by incident
- Visualize pre- and post-detection processes in chronological order

Agent operating in kernel mode
Agents operating in user mode will be stopped by the attacker. Agents operating in kernel mode are very difficult for attackers to stop working.
Variety of available logs
Since EDR detects from logs, the more log types, the more accurate the detection of threats. Capture and detect more than 200 types of logs, including process registry file network Windows event logs.
Enhanced response capabilities
Another pillar along with the detection of the EDR is the handling function. It provides the ability to isolate from the network and perform a variety of remote operations on endpoints. It works in kernel mode, so you can get information such as READ / WRITE files, writes to the registry, and memory dumps.
Visualized Process Tree
Improve analysis efficiency by graphically displaying the attack process in a tree.

| * | The Management screen displays a series of attacks as a process tree, along with threat ranking. |
| * | Intuitive visibility into the full picture of front-and-back attacks, plus drill-down for more detail, enables rapid investigation and response. |
| * | The picture is an image. |
Falcon OverWatch
- Threat hunting service from CrowdStrike security experts
- 24/7/365, expert manual monitoring of logs uploaded to the cloud to detect next-generation antivirus and EDR hard-to-detect attacks
- Notify and assist administrators in responding to high-urgency attacks

Security Expert
Experts from around the world use tools to isolate events that are uploaded from around the world and thoroughly suspicious to discover attacks that are difficult to detect only with tools that cannot be found with AI or machine learning. For those that are clearly under attack, notify the administrator directly by email. The experience and know-how accumulated by dealing with the latest attacks every day is reflected in the detection logic on the product side.
24/7/365 constant monitoring
Unlike general threat hunting, which consultants enter and investigate for a period of time, we constantly monitor your environment 24/7/365, expert manual monitors attacks by logs uploaded to the cloud which hard to detect by next-generation antivirus and EDR.
Additional Menu
Falcon Prevent
Falcon Insight
Firewall Management
Centralized management and operation of host firewalls.
CrowdStrike Falcon's common management console
Create, manage, and enforce policies for OS-native hosted firewalls such as Windows.
The policies created are delivered immediately and deploy and work in minutes.
Gain rapid visibility and enhancement across your environment to better protect against networked threats.

| * | The picture is an image. |
Falcon Prevent
Falcon Insight
Device Control
A service that provides visibility and control over the usage of devices connected to your internal environment.
You can view usage history of USB devices, export history, etc. You can also save and export these as logs. Allows policy-driven granular control of each device class.

Falcon Insight
Discover
Gain visibility into your computer, applications, user accounts, and more.
A service that allows you to properly manage endpoint hygiene.
You can visualize not only the host on which the agent is deployed, but also unmanaged hosts and NW devices in the same network as the host.
HW information, resources, encryption status, account permissions and usage status, failed logon enforcement,
Visualize from multiple perspectives, including the version of the application installed on the device and whether it is deployed.

| * | The picture is an image. |
Falcon Insight
Spotlight
A service that identifies vulnerabilities on a host, including OS and common application vulnerabilities.
Identify, record, and prioritize vulnerabilities in operating systems, common client- and server-based applications.
Not only [CVE (Common Vulnerabilities and Exposures)] but also [KB (Knowledge Base)] is also visible from the perspective, so vulnerability management can be easily performed.

| * | The picture is an image. |
Please consult a KDDI consultant.
Related Resources





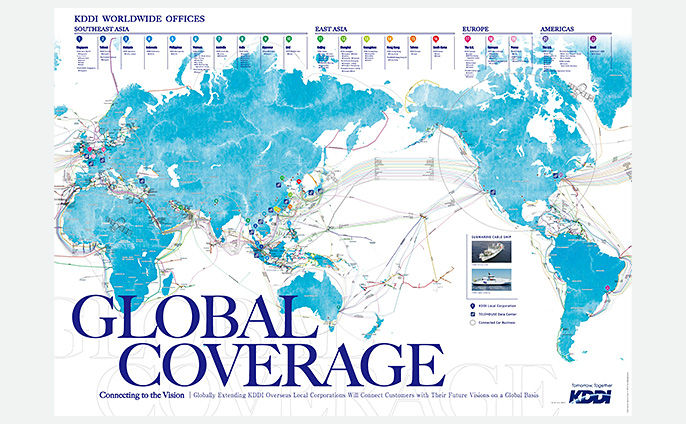

What is the best solution for your problem?
Please consult a KDDI consultant.